
What is Multifactor Authentication?
An authentication factor is something that is supplied to verify an identity – the most common example of an authentication factor is a password, a secret word used to authenticate yourself for access to an account. Multi-factor authentication is the requirement to supply several factors during authentication. This is often called “Two Factor Authentication” (2FA) as, most commonly, two factors are required, but it could, in some instances, be more and so MFA is the more general term.
Generally, these factors should be of a different type, so it’s not a good idea to use a “password” and a “secret word” since those are both knowledge-based challenges.
There are generally three types of factor:
- Something you know
- Something you have
- Something you are
“Know” covers knowledge-based challenges like password, secret words, PIN numbers, and that ‘secret’ handshake you and your friends used when you were kids. “Have” covers things that you have in your possession, such as a mobile phone or an authentication device such as a key card. “Are” covers aspects of your physical body, such as fingerprints and face scans.
Some people include other factor types such as “Somewhere you are”, where your geographic location is used as part of authentication. Others might include things such as “Something you do”, such as behavioural patterns.
As previously mentioned, the most commonly used authentication factor is a secret word, a password. However, users are generally awful at choosing good passwords and even if they do manage to make a good choice, they’re still an imperfect solution as there are additional problems such as passwords being “shoulder surfed” (That’s a slang term for stealing a password by simply watching someone type it in during login).
To minimise the risk of awful password choices, and the inherent weakness with passwords in general, some websites allow you to enable Multifactor Authentication. This can significantly reduce the likelihood of an account compromise through a credential attack. However, just as a password is harder to guess than a simple PIN number, not every authentication factor offers the same level of security.
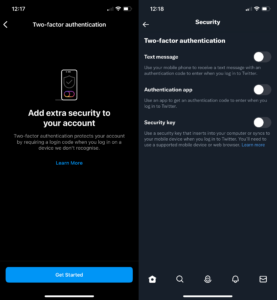
Some common options though:
- A PIN number received via text message, sometimes called an SMS-based one-time password (OTP).
- A PIN number received via email, sometimes called Email-based OTP.
- A notification sent to a mobile phone that requires you to click ‘accept’ to authorise the login.
- A PIN number displayed in a mobile app that changes frequently (e.g. every 30 seconds), sometimes called Time-based OTP (or TOTP for short).
- A physical device that you must connect in order to authenticate.
Different Levels of Security
Some of these options, although common, are troublesome. For example, any method that uses text messages can potentially be attacked via “SIM Swapping” – an exploitation method where, in short, an attacker tricks the user’s mobile phone provider into porting the target user’s phone number over to the attacker’s phone, allowing the attacker to receive the SMS codes.
That doesn’t mean SMS-based MFA cannot be used necessarily. Cybersecurity professionals are putting pressure on companies to offer more secure alternatives to SMS-based codes as they are more secure, but as a consumer if your only option is SMS-based, it’s better than nothing.
We reached out to a number of cybersecurity professionals and whilst a very small number did take the hard-line approach to SMS, saying that it should never be used for MFA, it seems that most took the line that if it’s your only choice as a consumer, it’s better than nothing.
Declan Doyle, Head of Ethical Hacking and Client Services at the Scottish Business Resilience Centre put it clearly when he said:
“MFA is probably the single best tool that an end user can use to protect against phishing and password attacks. My ‘hot take’ is that I think there is too many individuals in the cyber security industry claiming that SMS MFA is bad. The reason behind this is there are ways a hacker can hijack your sim and redirect the text messages to them, however these attacks are rare, and the benefits to MFA vastly outweigh the risks.”
— Declan Doyle, Head of Ethical Hacking and Client Services at the Scottish Business Resilience Centre (SBRC)
In regards to the most secure options, Google released some research back in 2019 that very clearly showed that hardware device “security keys” are the most effective, however on-device prompts were highly effective too – although potentially less effective for targeted attacks.
It should be noted though, that within the category of “on-device prompts” there are better and worse options. Some prompts simply require the user to click “approve” to allow the login, which can lead to issues. For example, it’s unlikely but possible that a user may accidentally hit approve by mistake when interacting with the app; there’s also the possibility that a user may get “MFA fatigue” where an attacker performs a large number of authentication attempts causing the user’s device to repeatedly prompt for authorisation – with the hope that the user will eventually just hit “accept”, due to lack of awareness of the attack type, or simply frustration.
To get around this “MFA fatigue” some authentication apps present a challenge, commonly the requirement to enter a six-digit PIN number, or similar, which greatly reduces this risk.
Given how effective MFA is at preventing account compromise is according to Google’s data, you might be wondering why you don’t see it very often. Well, an awful lot of websites offer it as an option, but it’s not highlighted – it’s just buried in the settings. For example, major social media platforms such as Twitter and Instagram have it, right there in the settings.
In summary, MFA is highly effective at preventing account compromise and you should strongly consider enabling it wherever it is supported. Not all MFA is the same, and you should generally prefer security keys over on-device prompts with challenges, and you should prefer on-device prompts with challenges over SMS-based MFA.
Account Recovery
One more thing I’d like to mention as we close out: account recovery. One of the major downsides to MFA is that it complicates account recovery. If you require a device to log in and you do not have that device available, you’ll have a problem.
In most cases this is easy to overcome, for example some authenticator apps allow you to backup your MFA seeds so that you can restore the app to another device. For other methods such as security keys, the vendors recommend you simply buy two and store one in a safe place in case you first is lost or damaged.
However, there are a couple of edge cases that can catch you out. From minor annoyances such as requiring an app on your phone to login, but your phone is out of power – a common problem for those of that spend a lot of time travelling, particularly sitting around in airports. Of course, you could just carry a battery pack to minimise this type of problem.
To more complex issues, such as trying to receive SMS-based PIN number whilst abroad and unable to receive text messages (for example as you’ve swapped out to a local SIM card whilst out of the country). Generally here, I’d point to the above guidance where we said other methods of MFA should be preferred ahead of SMS-based MFA – you wouldn’t have this problem with a security key or an app-based code for example.
The short answer with account recovery and MFA is that it likely won’t cause you a major problem as long as you think about it in advance, have a plan to recover your accounts in the event that your authentication device is not available, and test your plan occasionally.
That’s it!
Penetration Testing: Mix it up or stick with it?
After publishing yesterday’s article about how frequently you should get a penetration test, I inadvertently started a discussion on Twitter about another aspect of penetration testing delivery: Should you change providers, or you should stick with who you know? The argument I usually hear in favour of regularly changing security providers is that [...]| Play | Cover | Release Label |
Track Title Track Authors |
|---|
