Penetration Testing
Infrastructure Penetration Testing
External Infrastructure Penetration Tests assess the security exposure caused by internet facing devices and servers. Internal Infrastructure Penetration Tests are assessments of systems within an organisation’s perimeter, to determine the level of risk systems have from visitors, guest, contractors, and malicious insider threats.
We don’t just focus on vulnerability discovery, but we also give significant detail on remediating discovered issues and importantly, hardening systems against exploitation.
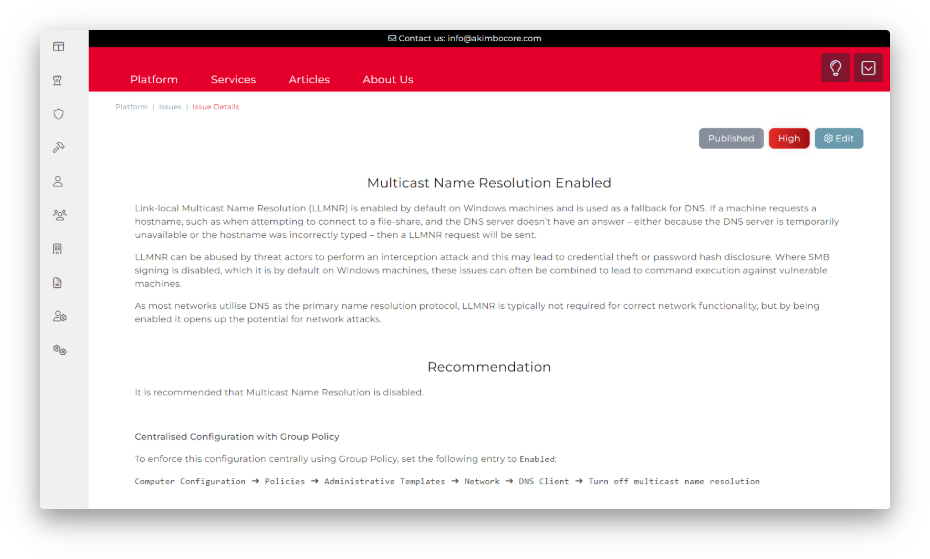
During the engagement you can track the findings within our web platform, allowing you to follow how the test is progressing but also to get a head start on remediating discovered issues. Once the assessment is complete, we will deliver a detailed report of findings and remediation guidance, as a record of your assessment.
Penetration Testing Methodology Summary
Mapping and Enumeration
The initial steps of the engagement include determining the attack surface for all in-scope systems, including host discovery, port scanning, service version scanning, and domain enumeration.
Vulnerability Identification and Confirmation
This stage includes the manual work performed by the tester to highlight security vulnerabilities; where authorised it will include the active exploitation of vulnerabilities to ensure that risks are appropriately graded, and false positives are removed. This includes service testing for issues such as known vulnerabilities, common and default misconfigurations, as well as manual testing for insecure services. It will also include testing of authentication systems, such as testing for weak passwords, default credentials, and insufficient account lockout policies.
Finally, network traffic will be assessed for weaknesses in-transit protection such insufficient cryptographic protection and insufficient protection against interception and relay attacks.
Privilege Escalation and Propagation
Privilege Escalation typically includes two main stages: escalation from domain user to local administrator, and escalation from local administrator to domain administrator. Where possible network propagation will be assessed to determine issues, such as reused administrative credentials.
This stage includes assessing local services for weaknesses such as insecure services paths and permissions, as well as testing for credentials in plaintext, token impersonation, and administrative session interception.
Post Exploitation
Once a compromise is achieved additional attack vectors are assessed, credential audits are performed, and risk assessments are performed to determine what level of system access could be achieved and the level of skill required by the attacker to perform the exploitation.
Remediation
We don’t just focus on vulnerability discovery, but we also give significant detail on remediating discovered vulnerabilities and importantly, hardening systems against exploitation.

In addition to Penetration Testing we also offer Cybersecurity Training and Cybersecurity Consultancy to offer a comprehensive suite of cybersecurity services.
Cybersecurity Training
Akimbo Core deliver cybersecurity workshops all around the UK, as well as remotely. Our workshops cover a range of topics from technical subjects such as how to get the most out of cybersecurity testing, to security awareness issues within businesses.

Cybersecurity Consultancy
From security architecture to security assessment, we offer a wide range of services to ensure the protection of your assets. We use a highly flexible methodology to ensure that our services are fully aligned to your needs, delivered by a bespoke team with the precise skills and depth of experience needed to understand your issues and then effectively deliver the desired outcome. With our security assurance services, you can have peace of mind knowing that your systems and data are well-protected.

WE CAN FIND YOUR VULNERABILITIES
BEFORE YOU ARE BREACHED
GET IN TOUCH
© 2024 Akimbo Core Ltd
| Play | Cover | Release Label |
Track Title Track Authors |
Page | Buy | Delete |
|---|