Link-Local Multicast Name Resolution (LLMNR) and NetBIOS-Name Service (NBT-NS) are name resolution protocols that are enabled by default on Windows machines. They’re both used as a fallback for DNS. If a machine requests a hostname, such as when attempting to connect to a file-share, and the DNS server doesn’t have an answer – either because the DNS server is temporarily unavailable or the hostname was incorrectly typed – then an LLMNR request will be sent, followed by an NBT request. LLMNR is a multicast protocol and NBT-NS is a broadcast protocol.
Therefore, an attack can take place where an attacker responds to these requests with illegitimate requests. For example, directing the requesting user to connect to the attacker’s machine where an authentication attempt will be made – disclosing hashed credentials for the targeted user.
There are several ways to perform this attack but an easy to use tool for it is Responder; there are two versions – one from SpiderLabs and one from Lgandx. The version at SpiderLabs is deprecated.
Responder is very simply to use and includes a sensible default configuration meaning that it can be run by simply including the “-I” flag and setting the name of the network interface to run on:

Responder starting up on the interface called eth0
At this point, just wait! If a user mistypes a machine name, if the DNS server is temporarily unavailable, or if there’s another similar DNS failure then users will begin to multicast their name requests and Responder will intercept them. If the credentials are sent in plaintext they will be displayed to the screen, or more likely, you’ll receive hashed credentials for something like a file-share connection:
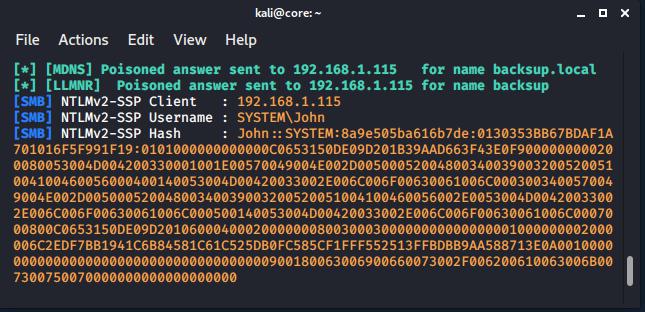
Hashed user credentials are captured.
At this point, these credentials could be cracked using a common tool like John the Ripper or Hashcat. If you need to crack them very quickly, then our post on Hashcracking with AWS could help!
Oh and don’t forget to read how to Fix LLMNR and NetBIOS-NS Spoofing.
That’s it!
Read More
An Introduction to IPv6
Internet Protocol Versions IPv6 is not new, RFC1883 discussed the protocol back in 1995. However, it has been updated several times, becoming a Draft Standard with RFC2460 in 1998, and an Internet Standard with RFC8200 in 2017! If you’re wondering if there was an IPv5 the answer is sort of, in the Experimental Internet Stream Protocol, Version [...]| Play | Cover | Release Label |
Track Title Track Authors |
|---|
